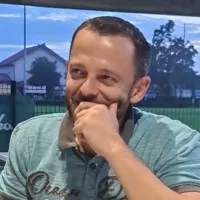
Aleksandar Kosanovic
Software developer

Connect with Aleksandar Kosanovic to Send Message
Connect
Connect with Aleksandar Kosanovic to Send Message
ConnectTimeline
About me
System engineer/Vulnerability Assessment/Penetration Tester at KING ICT
Education

MIOC
-
OS Otok
-
CISCO academy in Zagreb/Croatia
2007 - 2008CCNA Cisco Certified Network Associate
University of Zagreb / Sveučilište u Zagrebu
1996 - 2003B.Sc.E.E. Telecommunication and Informatics
Experience

Siemens d.d.
Jan 2004 - Aug 2005Software developer- have worked as Software Developer for Data Services team in Zagreb, Croatia- have participated in all phases of process of developing and maintening features (old and new) of software for Mobile Switching Centre (CP part) : analysis, design, coding, testing (simulator), verification

Ericsson Nikola Tesla
Aug 2004 - Jan 2010- working on international projects (till now 23 of them)- working on network design based on MSS (Mobile softswitch solution) CS based- specialized on MGWs and MSC-Servers- complete hardware allocation for MGWs and MSC-Servers, defining interfaces, terminations, type of transmission (TDM, ATM and IP), ATM design (VCs and VPs, traffic descriptors, AAL2 and AAL5 specifics), Virtual MGWs, MSC in Pool concept- working on dimensioning the mobile core network nodes - worked with all types of transmission: TDM, ATM and IP Show less
IMS Solution Architect
Aug 2008 - Jan 2010Network Design and NPI manager
Aug 2004 - Aug 2008

Ericsson Nikola Tesla
Apr 2010 - May 2023- Vulnerability Assessment/Analysis - systematic approach used to analyze the security posture of a product. It combines: * Test execution: > vulnerability testing (PRIO 1) – information collection, network discovery, port scanning and vulnerability scanning > robustness tests (PRIO 2) – denial of service attacks and protocol fuzzing... > penetration testing (PRIO 3) – manual web (Burp suite, OWASP top ten..), manual ad hoc (not just web), brute force attacks, Man in the Middle attacks... * Test result analysis > gather, analyse and validate the findings > write VA report - identifies the system or node vulnerabilities, their severity and their recommended mitigation action- introduced to common attack vectors- Tools used: * Codenomicon Defensics - used for protocol robustness test and security testing, fuzz testing (fuzzing) * Nessus – vulnerability scanner * nmap – port and vulnerability scanner * hping3 – TCP/IP packet assembler/analyzer * wireshark - network protocol analyzer * OpenVas – Open Source vulnerability scanner and manager vulnerability assesment suite * zenmap – official nmap security scanner GUI * Metasploit Framework and Armitage - contains a suite of tools that you can use to test security vulnerabilities, enumerate networks, execute attacks, and evade detection * OWASP ZAP - web application security scanner * IXIA - traffic generator * Scapy and other packet crafter tools * t50 stress test tool * thc-ssl-dos - DoS Tool Against Secure Web-Servers and for Testing SSL-Renegotiation * Burp suite - Application Security Testing Software * Nikto - Web Server Scanner * Kali Linux penetration testing tools Show less
Vulnerability Assessment Tester
Jun 2016 - May 2023Software engineer
Apr 2010 - Jun 2016

KING ICT
May 2023 - nowSystem engineer/vulnerability assessment/penetration tester
Licenses & Certifications
- View certificate

Complete Website Ethical Hacking and Penetration Testing
UdemyOct 2022 - View certificate

XSS Survival Guide
UdemyNov 2022 - View certificate

Web Application Penetration Tester
INEDec 2023 
Practical Web Application Security and Testing
TCM SecuritySept 2022- View certificate
CompTIA Network+
CybraryNov 2020 - View certificate
Offensive Penetration Testing
CybraryDec 2020 - View certificate
Penetration Testing and Ethical Hacking
CybraryAug 2020 - View certificate

Python for Penetration Testers
UdemyApr 2020 
Web Application Penetration Testing
The Offensive LabsJan 2023- View certificate

Python Basics
UdemyMay 2020 - View certificate
Cyber Network Security
CybraryNov 2020 - View certificate

Ethical Hacking Using Python Course
UdemyMay 2020 - View certificate

The Complete Python Hacking Course: Beginner to Advance
UdemyNov 2020 - View certificate

Practical Ethical Hacking - The Complete Course
UdemyMay 2020 - View certificate

The Ultimate BAC and IDOR
UdemyMar 2023 - View certificate

Jr Penetration Tester Learning Path
TryHackMeJul 2022 - View certificate

Junior Penetration Tester
INEAug 2024 - View certificate

CompTIA PenTest+ (PT0-001): 2 Survey the Target
LinkedInMay 2020
Recommendations

Janan botrie
Executive Director at Claritas Centre SantéLaval, Quebec, Canada
Sanjay singh negi, ms, mch, febs, febs, facs
Principal Consultant and Head, GI-HPB Surgery, GI Oncosurgery, Laparoscopic - Robotic Surgery and Li...Delhi, India
Amira ben elkbaier
Data Science Masters student at ELTE in Budapest, HungaryBudapest, Budapest, Hungary
Jj hossi ceng miet cmareng mimarest
Subsea Engineering Section Lead - Azule-EnergyAngola
Rui flora
Senior Manager - Data & Analytics at IDCLisboa, Lisbon, Portugal
Omkarnath salle
Consultant Specialist at HSBCPune, Maharashtra, India
Ichsan namora lubis
Senior Relationship Manager at TokopediaJakarta, Jakarta, Indonesia
Raphael arceo
Material Science and Engineering - Licensed Metallurgical EngineerBataan, Central Luzon, Philippines
Chevwin chu
Senior Manager at Galaxy Entertainment GroupMacao SAR
Jorge pérez marcos
Director ComercialMonterrey, Nuevo León, Mexico
Nuur mahamed
network engineer Cable Technician at Kelly GroupBirmingham, England, United Kingdom
Yalçın ereli, pmp, msc., mmba
Sözleşme Yöneticisi / Contract ExecutiveKaradeniz Ereğli, Zonguldak, Türkiye
Pramod maharudra junja
I'm actively looking for a job for SAP MM Associate Consultant (Immediate joiner)Bengaluru, Karnataka, India
Alfredo lopez
Information Technology and Services ProfessionalHouston, Texas, United States
Bill lee
Infrastructure Manager at Poly Real Estate Investment Consultancy Co., Ltd.Guangzhou, Guangdong, China
Adinugraha irman
Resident Network security Engineer di WAHANA CIPTA SINATRIA, PTDepok, West Java, Indonesia
Mohamad ettefagh
Director at EnstoaColumbus, Ohio Metropolitan Area
Javier garcia
Executive Protection Agent | Former Marine Embassy Security Guard | BA in International Relations | ...Los Ángeles, California, Estados Unidos
Aline s.
VP of Operations at LendingOne, LLCFort Lauderdale, Florida, United States
Alisia scalzullo
Registered Clinical Dietitian & SA Lactation ConsultantJohannesburg Metropolitan Area
...
 Deep Enrich
Deep Enrich